Infrastructure as Code (IaC) Tools, Part 2: Choosing the Right Tool
In this article, discover practical approaches for choosing the best IaC tool for your cloud infrastructure needs.
This article builds upon the previous blog, providing further insights into the best practices and challenges discussed in Part 1. It offers tangible approaches to assist you in selecting the ideal Infrastructure as Code (IaC) tool for your cloud infrastructure needs. The article will outline practical considerations for evaluating different tool options and carefully weighing the trade-offs involved. By referencing the guidance on tool categories and ecosystem tools provided in Part 1, this blog post aims to support your teams in making well-informed decisions when choosing the most suitable IaC tool to fulfill their unique cloud infrastructure requirements.
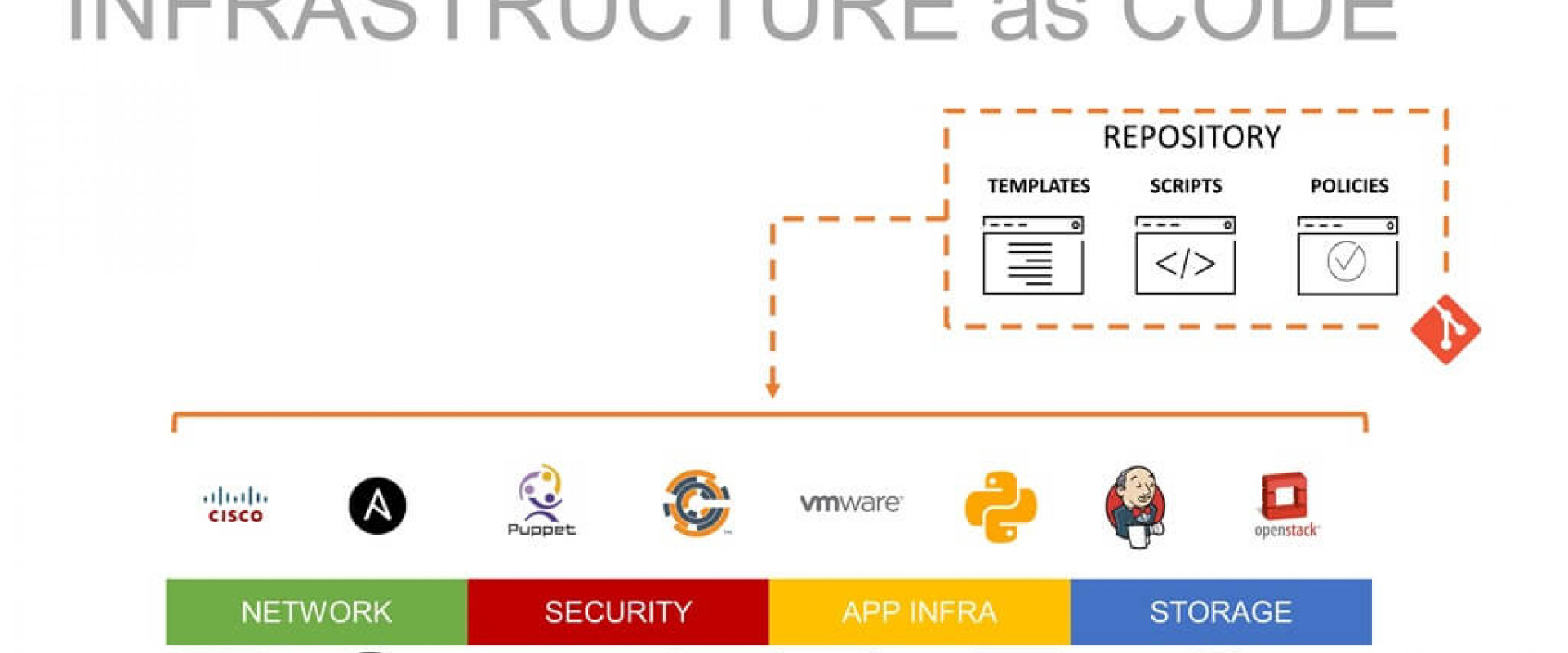
Classification of Tools
IaC tools are categorized based on the purpose of the tools and how they interact with the target systems.
Tools for Managing Infrastructure Resources
Mutable and immutable are two different approaches to managing infrastructure using Infrastructure as Code (IaC) tools.
Mutable IaC Tools
Mutable IaC tools allow making changes to existing infrastructure resources. With mutable IaC, the tool manages the lifecycle of resources, including updates and modifications. When a change is made to the infrastructure code, the tool applies the necessary updates to the existing resources to bring them in line with the desired state.
Mutable IaC tools typically track the current state of the infrastructure and apply incremental changes to achieve the desired configuration. This means that the infrastructure resources can be modified over time, and the tool handles those changes by updating or modifying the existing resources.
Examples of mutable IaC tools include Ansible, Chef, and Puppet. These tools often have built-in features for managing the configuration and state of individual systems, and they can apply changes and updates to those systems as needed.
Immutable IaC Tools
Immutable IaC tools follow a different approach by treating infrastructure resources as immutable objects. Instead of modifying existing resources, immutable IaC tools create new resources with each change. When changes are made to the infrastructure code, the tool provisions a new set of resources that reflect the desired state, while the old resources are replaced or removed.
Immutable IaC promotes the idea of recreating the infrastructure from scratch rather than modifying it incrementally. It ensures that the infrastructure is always in a known and predictable state, as any changes result in a completely new set of resources.
Examples of immutable IaC tools include Terraform, AWS CloudFormation, Azure Resource Manager, and Google Cloud Deployment Manager. These tools focus on provisioning and managing infrastructure resources by creating new instances or services based on the desired configuration.
Both mutable and immutable approaches have their advantages and use cases. Mutable IaC can be beneficial in scenarios where incremental changes are needed, while immutable IaC provides a more consistent and predictable infrastructure state. The choice between mutable and immutable IaC depends on factors such as the project requirements, desired level of control, and the nature of the infrastructure being managed.
Tools for Managing and Provisioning Infrastructure Resources
Declarative and imperative are two different approaches to defining infrastructure configuration and management in Infrastructure as Code (IaC) tools.
Declarative Approach
In the declarative approach, you define the desired state of your infrastructure without specifying the detailed steps to achieve it. You focus on describing what the infrastructure should look like rather than how to get there. You declare the desired configuration, and the IaC tool determines the necessary actions to bring the infrastructure into the desired state.
With a declarative approach, you typically work with templates or configuration files that describe the desired infrastructure configuration. The IaC tool compares the current state of the infrastructure with the desired state defined in the template and applies the necessary changes to make them consistent.
Declarative IaC tools include Terraform, AWS CloudFormation, Azure Resource Manager Templates, Google Cloud Deployment Manager, and Heat. These tools use a declarative language or template format to specify the infrastructure configuration.
Imperative Approach
In the imperative approach, you specify the detailed steps and instructions for achieving the desired infrastructure state. You define the sequence of operations and the specific actions to be taken to configure and manage the infrastructure.
With an imperative approach, you typically work with scripting or programming languages to define the infrastructure configuration. You write procedural code that specifies the exact steps to be executed by the IaC tool to configure and manage the infrastructure.
Imperative IaC tools include tools like Ansible, Chef, and Puppet. These tools often use domain-specific languages (DSL) or configuration files to define infrastructure and manage it through procedural code.
The declarative approach focuses on describing the desired state of the infrastructure, while the imperative approach focuses on specifying the steps and actions required to reach that state. The choice between declarative and imperative IaC depends on factors such as the complexity of the infrastructure, desired level of control, and the skills and preferences of the team using the IaC tool.
Tools Based on Interaction With Target Systems
Agent and agent-less are two different approaches to implementing Infrastructure as Code (IaC) tools.
Agent-Based IaC Tools
Agent-based IaC tools require the installation and configuration of an agent or software component on the target infrastructure resources. The agent acts as a communication channel between the IaC tool and the managed resources. It is responsible for executing commands, collecting information, and reporting back to the IaC tool.
The agent is typically installed on each target system or instance that needs to be managed. It establishes a connection with the IaC tool, which can then remotely manage and configure the resources by communicating with the agent.
Examples of agent-based IaC tools include Ansible, Chef, and Puppet. These tools rely on agents that need to be deployed on the target systems, and they use the agents to execute configuration instructions and manage the resources.
Agent-Less IaC Tools
Agent-less IaC tools, as the name suggests, do not require the installation of any agents on the target infrastructure resources. Instead, they utilize existing protocols and interfaces to remotely manage and configure the resources.
Agent-less IaC tools typically rely on protocols like SSH (Secure Shell) or WinRM (Windows Remote Management) to establish a connection with the target systems. They execute commands and configurations remotely, without the need for an intermediary agent.
Examples of agent-less IaC tools include Terraform and some capabilities of Ansible. These tools can connect to the target resources using standard protocols, authenticate using credentials, and remotely manage the infrastructure without installing any additional software components.
Both agent-based and agent-less approaches have their advantages and considerations. Agent-based tools often provide more extensive capabilities and control over managed resources, but they require the deployment and maintenance of agents. Agent-less tools, on the other hand, have a simpler setup process but may have certain limitations in terms of functionality or compatibility with specific systems.
The choice between agent-based and agent-less IaC tools depends on factors such as the target infrastructure, security requirements, ease of deployment, and the specific capabilities needed for managing the resources effectively.
Comparison of Tools
Here is the comparison of more popular IaC tools in the market which helps to decide the tool appropriately.
|
ANSIBLE |
CHEF |
PUPPET |
TERRAFORM |
|
|
Open Source |
Yes |
Yes |
Yes |
Yes |
|
Configuration Language |
YAML |
Ruby |
DSL |
HashiCorp Configuration Language (HCL) |
|
Architecture |
Agentless |
Agentless Client-Server with Chef-Client |
Master-Agent |
Agentless Client-Server |
|
Approach |
Procedural and imperative language (YAML) |
Declarative and procedural language (Chef DSL or Ruby) |
Declarative language (DSL) |
Declarative language (HCL) |
|
Supported Platforms |
Linux, Unix, Windows |
Linux, Unix, Windows |
Linux, Unix, Windows |
Cloud providers, Infrastructure providers |
|
Use Case |
Configuration Management, Application Deployment, Continuous Delivery |
Infrastructure Automation, Configuration Management |
Configuration Management, Infrastructure Automation, Continuous Delivery |
Infrastructure Orchestration |
|
Community Support |
Large community with good documentation |
Large community with good documentation |
Large community with good documentation |
Growing community with good documentation |
|
Learning Curve |
Easy to learn and use |
Easy to learn and use |
Steeper learning curve |
Moderate learning curve |
|
Scalability |
Easily scalable |
Easily scalable |
Easily scalable |
Highly scalable |
|
Plugins |
Large library of pre-built modules |
Large number of pre-built cookbooks |
Large library of pre-built modules |
Large number of pre-built providers and modules |
|
Integration |
Works well with other tools in the DevOps toolchain |
Good integration capabilities with other tools |
Good integration with other tools |
Good integration with other tools |
|
Cost |
Free and open source |
Free and open source |
Free and open source |
Free and open source |
Conclusion
Infrastructure as Code (IaC) tools provide diverse methods for managing and provisioning resources. Deciding between mutable and immutable approaches, declarative and imperative tools, or agent-based and agent-less tools depends on the specific requirements of the project. When choosing an IaC tool, teams should take into account factors such as supported platforms, community support, scalability, and cost. Popular IaC tools like Ansible, Chef, Puppet, and Terraform offer distinct features and capabilities. By conducting a careful comparison of these tools, organizations can make an informed decision and select the most suitable option for their needs.
We Provide consulting, implementation, and management services on DevOps, DevSecOps, DataOps, Cloud, Automated Ops, Microservices, Infrastructure, and Security
Services offered by us: https://www.zippyops.com/services
Our Products: https://www.zippyops.com/products
Our Solutions: https://www.zippyops.com/solutions
For Demo, videos check out YouTube Playlist: https://www.youtube.com/watch?v=4FYvPooN_Tg&list=PLCJ3JpanNyCfXlHahZhYgJH9-rV6ouPro
If this seems interesting, please email us at [email protected] for a call.
Recent Comments
No comments
Leave a Comment
We will be happy to hear what you think about this post