What Is Zero Trust Security?
Zero Trust security is an IT security framework that treats everyone and everything to be hostile (in a good way!).
Automation has been around for decades in various forms, and it’s only now that we’re starting to see its full potential. Automating the software development lifecycle (SDLC) can significantly improve quality assurance, developer productivity, and reductions in time spent on specific tasks. Companies have started to invest more in security practices throughout their SDLCs to protect their data and prevent malware attacks.
Security practices are continuously evolving as the industry changes. There has been a shift from traditional security practices where security was considered to be outside of the development team’s scope, to making security a priority in the SDLC. Adopting a shift-left mentality is on the rise, which means starting with security before the development phase of the SDLC. This has helped companies adopt a more agile approach to handling cybersecurity.
What Is Zero Trust Security?
Zero Trust security is an IT security framework that treats everyone and everything to be hostile (in a good way!). Thus the Zero Trust security model grants least privileged access to all IT resources, meaning no one should be trusted for anything other than what they have been explicitly granted access to. Instead, only the verified and authorized networks, apps, users, IP addresses, and devices are allowed inside the network by following strict protocols.
The attainment of this Zero Trust framework involves advanced and secured technologies to verify the user’s identification and achieve the system’s security. Some notable technologies used to accomplish this are role-based access control, multifactor authentication, identity and access management (IAM), identity protection, and endpoint security technology. Furthermore, the strict and dynamic user authentication approach is enforced before granting any access.
In addition, constant potential threat scanning and detection are carried out.
In this article, we will focus on Zero Trust security and its importance regarding the software development lifecycle.
Why Security in SDLC?
Every company wants to release new features to their customers faster, and security needs to meet the pace of innovation. Also, organizations are moving their workloads to the cloud, taking advantage of cloud computing services, and the cloud provides for dynamic scaling. It has become obligatory to scale security to match the scale of the cloud. Companies today cannot allow services to go down even for a second, and hence security becomes crucial in automatic incident response remediation.
The cost of fixing a bug in production will upset your customers and create a lot of overhead with the development team, and hence it is highly prescribed by security experts to have security checkpoints at each stage of your SDLC.
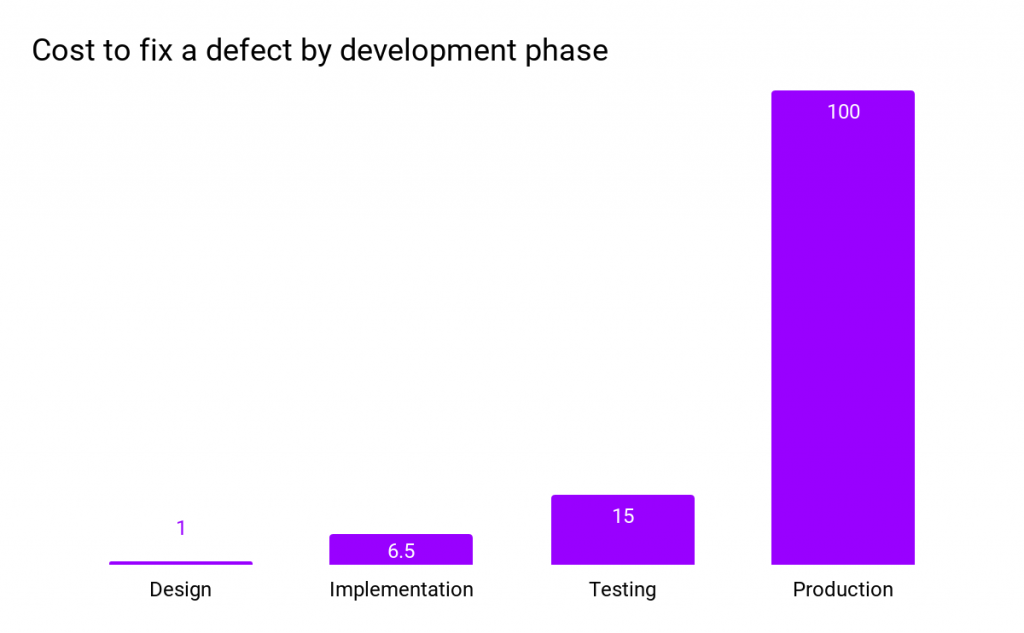
Cost to fix a defect by development phase: IBM System Science Institute: Relative Cost of Fixing Defects
To successfully and securely leverage automation, there needs to be an added emphasis on security throughout the SDLC. That is where DevSecOps comes in as an integrated mindset for cloud native tech to unify development, operations, and security as one process in the SDLC. It advocates a shift-left approach promoting security at a very early stage of the SDLC.
Challenges of Implementing DevSecOps
There are many challenges to implementing security into the DevOps workflows. Here are a few of the main ones:
•DevOps is a fast-paced game: As DevOps focuses mainly on fast development, deployment, and releases, it becomes challenging for security to get in line with this pace of the fast-moving race.
•Siloed team approach: Security teams usually use different toolsets and processes, and they often lack complete SDLC visibility. This consideration of dev and sec as two separate teams becomes challenging.
•Scalability and integration: With the invention of containerization and creating virtual VMs, DevOps gives away many new attack surfaces to attackers. Various tools and technologies such as Jenkins, Docker, etc., add different security challenges while scaling and can create layers (literally) of complexity.
•Skillset: The scarcity of security principles, proof of concept, and skillset in the DevOps world make hiring true security professionals challenging. Also, enterprises often tend to neglect security teams and not involve them in major decisions, whether it is selecting a new platform or a tool, updating policies, etc., and hence the holistic vision of keeping security at utmost priority gets diluted easily.
•Poor tool selections: Selecting inadequate tools and making poor decisions end up becoming liabilities. This can be done by making the security team a part of the design considerations, tools selection, policymaking, compliance, governance, etc.
Security Best Practices in SDLC
Here are some tips for implementing Zero Trust security in your DevOps pipeline:
- Implement DevSecOps as a base of your SDLC and make the shift-left approach a must.
- Make Software Bill of Materials (SBOM) mandatory whenever working with third-party tools and vendors.
- Have regular security training, instill security awareness and ownership across your developer and operations teams.
- Have security checkpoints at each stage of your SDLC and validate that only good code and no confidential data or secrets are exposed to the outside world.
- Integrate static code analysis into the build process.
- Have a threat modeling plan to identify and mitigate the potential security risks involved in the development process.
- Make continuous security aforethought. Utilize security and compliance best practices and adopt continuous improvement strategies.
- Use security tools that integrate well with your SDLC and easily automate the security and governance with little or no human intervention.
- Ensure your tool suite comprises a robust security vulnerability detector and a universal software composition analysis solution.
- Have strong security threat response management policies to address any security threats if they occur.
- Have access control policies with clear boundaries on access rights, roles, and responsibilities to clear conflict between the teams.
Notable Security Tools
JFrog Xray: JFrog‘s Xray is a known security vulnerability tool that scans all of your open source software artifacts and their dependencies for vulnerabilities and licenses compliance issues. It scans repositories, builds packages, and container images. It detects compromised licenses and any violations in your software components ensuring your end-to-end software lifecycle becomes as smooth as possible.
SonarQube: SonarQube is an open-source tool for continuous code inspection. It collects and analyzes source code and provides reports on the code quality of your projects. With regular use, SonarQube guarantees a universal standard of coding within your organization while ensuring application sustainability.
Vdoo: Vdoo is a highly recommended security tool that enables security teams to reveal and lessen the software risks involved in the applications, containers, embedded, IoT, and edge devices. With Vdoo, teams responsible for security can do automated and configuration security audits within minutes. [Note: JFrog recently acquired Vdoo to enhance its security game in the cloud-native space.]
Aqua Security: The Aqua Security Platform implements security automation across the whole application lifecycle to secure the build, cloud infrastructure, and workloads wherever they are deployed.
WhiteSource: WhiteSource is the license compliance management platform that ensures the teams can efficiently manage and trust their open-source assets. It detects and remediates security and compliance issues throughout the SDLC. It alerts and helps developers find and fix the issues whenever they occur.
Logz.io: Logz.io is built to provide more reliable observability into the systems through log management and log analytics services. The tool provides a centralized platform for security and operations teams, specially intended for cloud-native environments.
Secure Your SDLC
Security becomes crucial at every point of the SDLC to reduce the risk of human error. It is believed in most of the companies that “shifting left” and making security everyone’s job will improve the security part of the whole SDLC. But is that it? There is a lot more to securing the SDLC than just making security everyone’s job.
Here are some points on how to get started with securing your SDLC:
- Create solid secure coding best practices, guidelines, and frameworks to be incorporated across the SDLC by developers.
- Make security training a must for every developer who joins your company.
- Use best-of-the-breed tools for security vulnerabilities, static code analysis, end to end supply chain protection.
- Make code review, scanning, penetration testing, and architecture analysis an integral part of the development effort.
- Integrate security into your CI/CD pipeline through tools such as JFrog Xray, Vdoo, SonarQube, etc.
- Make sure to have a security checklist for every tool you incorporate in your SDLC. For example, if you are using platforms like Docker and Kubernetes, make sure to use only the official Docker images and have high-level cluster security for your workloads on Kubernetes.
- If you are using open source tools in your SDLC, make sure to use software composition analysis (SCA) tools to analyze open-source code, libraries, and dependencies, etc.
- Have a custom dashboard or tools that help you see what’s happening across your SDLC in a single pane of glass. Maybe, incorporate the monitoring tools such as Dynatrace, Nagios, or Datadog to get this information.
It is recommended to use tools that have a holistic approach to security in a single pane of glass — an end-to-end platform that connects all the dots and establishes a Zero Trust security system that is hard to penetrate for an attacker to gain access. When it comes to SDLC, your binaries and all the dependencies form vital input data for further steps.
To start, you’ll need a process and a toolset that secures binaries all the way to the edge consolidates security data for efficient decision-making and an end-to-end delivery system with the highest integrity.
Conclusion
No matter what industry and stage you are at in your cloud-native journey, zero trust principles have become a must and are being adopted by small and medium to large enterprises to ensure their systems are always highly secure and available. Ensuring a solid foundation on security by implanting security principles, best practices, and tools makes it possible to mitigate security threats.
We Provide consulting, implementation, and management services on DevOps, DevSecOps, Cloud, Automated Ops, Microservices, Infrastructure, and Security
Services offered by us: https://www.zippyops.com/services
Our Products: https://www.zippyops.com/products
Our Solutions: https://www.zippyops.com/solutions
For Demo, videos check out YouTube Playlist: https://www.youtube.com/watch?v=4FYvPooN_Tg&list=PLCJ3JpanNyCfXlHahZhYgJH9-rV6ouPro
If this seems interesting, please email us at [email protected] for a call.
Automate Server Hardening with AutomateCIS
Safeguarding IT systems against cyber threats would take lots of time and required many meetings between IT and Security to debate which configuration settings.
Center For information security(CIS) has developed CIS Benchmarks for operating systems and cloud platforms. But applying them to individual systems and auditing their current state is impracticable.
AutomateCIS is a scalable platform to Audit your Servers against CIS Benchmarks, Remediate the failed audits, and rollback the remediation just in case the remediation is causing issues on your application
Try AutomateCIS Free here: (https://www.zippyops.com/automatecis)
Relevant Blogs:
Recent Comments
No comments
Leave a Comment
We will be happy to hear what you think about this post