The Role of Threat Modeling in Software Development: A Cybersecurity Perspective
Discover how threat modeling enhances software security, reducing cybersecurity risk in this insightful cybersecurity perspective.
In today's digitally interconnected world, software plays an integral role in our daily lives. From online banking and e-commerce to healthcare and transportation, software applications are at the heart of our technological infrastructure. However, with the increasing reliance on software, the risks associated with cyber threats have also grown exponentially. This is where threat modeling steps in as a crucial component of software development, providing a proactive approach to cybersecurity. In this blog, we will delve into the concept of threat modeling and explore its pivotal role in safeguarding software from cyber threats.
Understanding Threat Modeling
Threat modeling is a systematic approach to identifying and mitigating security threats early in the software development process. It is essentially a risk management process that helps software developers anticipate potential vulnerabilities and security weaknesses in their applications. By analyzing and understanding potential threats, development teams can proactively address security concerns, reducing the likelihood of costly security breaches in the future. Threat modeling is an essential practice in software development, playing a pivotal role in reducing cybersecurity risk.
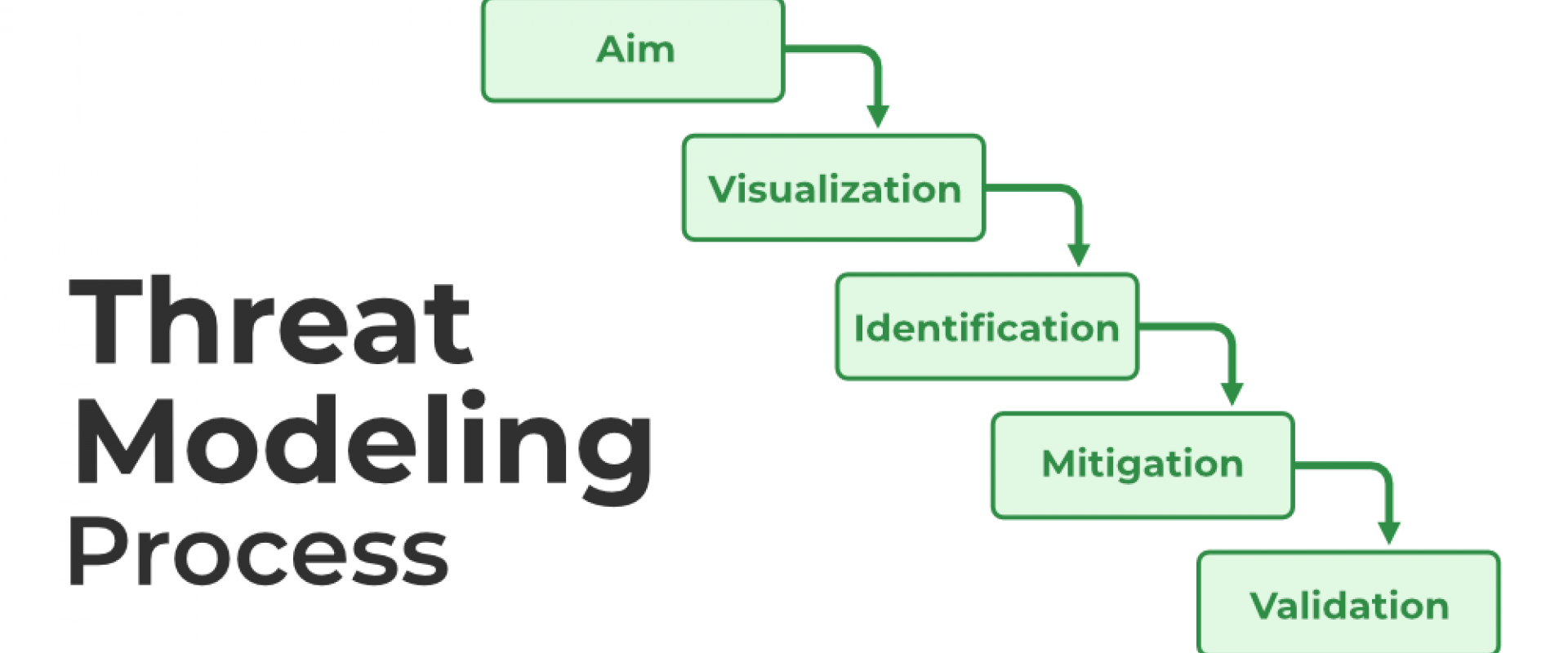
The threat modeling process typically involves the following key steps:
1. Asset identification: First and foremost, developers identify what needs to be protected within the software. This includes sensitive data, user accounts, and any other assets that could be targeted by malicious actors.
2. Threat identification: Once assets are identified, the team assesses potential threats that could compromise these assets. Threats can come in various forms, such as unauthorized access, data breaches, denial-of-service attacks, and more.
3. Vulnerability analysis: After identifying threats, the team evaluates the vulnerabilities within the software that could be exploited by these threats. Vulnerabilities may arise from coding errors, design flaws, or misconfigurations.
4. Risk assessment: This step involves quantifying the risk associated with each identified threat and vulnerability. It helps prioritize which security issues should be addressed first, taking into account potential impact and likelihood.
5. Mitigation Strategies: Finally, the development team devises mitigation strategies to address the identified risks. These strategies can include implementing security controls, improving coding practices, and conducting security testing.
Benefits of Threat Modeling
Now that we have a basic understanding of threat modeling let's explore the significant benefits it offers to software development from a cybersecurity perspective:
1. Early detection of vulnerabilities: Threat modeling allows developers to identify security issues at the design stage of software development, making it easier and more cost-effective to address these problems before they become ingrained in the code.
2. Reduced security risks: By systematically identifying and mitigating threats and vulnerabilities, threat modeling significantly reduces the risk of security breaches, data leaks, and cyberattacks.
3. Cost savings: Detecting and addressing security issues early in the development process is far less expensive than dealing with the fallout of a security breach or attempting to patch vulnerabilities in a production system.
4. Compliance and regulations: Many industries have stringent regulatory requirements related to data security. Threat modeling helps organizations demonstrate their commitment to compliance by actively addressing security concerns.
5. Improved security awareness: The process of threat modeling promotes a culture of security awareness among developers and other stakeholders, fostering a proactive approach to cybersecurity throughout the organization.
6. Enhanced customer trust: When customers and users see that an application has undergone rigorous threat modeling and security testing, they are more likely to trust it with their sensitive information.
Common Threat Modeling Approaches
There are several established threat modeling approaches that organizations can adopt, including:
1. STRIDE: This Microsoft-developed approach focuses on six types of threats: Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege.
2. DREAD: DREAD stands for Damage, Reproducibility, Exploitability, Affected Users, and Discoverability. It's a risk assessment model that assigns scores to each of these factors to prioritize threats.
3. Attack Trees: Attack trees are a graphical representation of potential attack scenarios, showing how various threats and vulnerabilities can be chained together to achieve a specific malicious goal.
4. OWASP Top Ten: The Open Web Application Security Project (OWASP) publishes a list of the top ten web application security risks. This can serve as a valuable framework for threat modeling in web applications.
Conclusion
The role of threat modeling in software development is crucial for identifying potential vulnerabilities and security risks, helping to enhance the overall security of the application or system, as emphasized in various educational platforms like Illumeo. In an age where software vulnerabilities can lead to devastating data breaches and security incidents, threat modeling is no longer an optional step in the software development process; it's a necessity. By systematically identifying and mitigating security threats and vulnerabilities early on, organizations can build more secure software, protect sensitive data, and enhance their reputation in an increasingly digital world. Embracing threat modeling as a fundamental aspect of software development is a proactive step towards ensuring robust cybersecurity and safeguarding the digital landscape for both businesses and users alike.
We Provide consulting, implementation, and management services on DevOps, DevSecOps, DataOps, Cloud, Automated Ops, Microservices, Infrastructure, and Security
Services offered by us: https://www.zippyops.com/services
Our Products: https://www.zippyops.com/products
Our Solutions: https://www.zippyops.com/solutions
For Demo, videos check out YouTube Playlist: https://www.youtube.com/watch?v=4FYvPooN_Tg&list=PLCJ3JpanNyCfXlHahZhYgJH9-rV6ouPro
If this seems interesting, please email us at [email protected] for a call.
Relevant Blogs:
Strengthening Your Web App Security: Preventing SQL Injections
Azure PAM: How to Manage Access With Azure Bastion and Azure PIM
Utilizing Apache Spark for Azure Network Security Group Management
Overcoming Challenges in UI/UX Application Modernization
Recent Comments
No comments
Leave a Comment
We will be happy to hear what you think about this post